Cutting-Edge BQT Biometrics Australia for Boosted Security and Safety And Security
Wiki Article
The Future of Safety: Checking Out the most up to date Trends in Electronic Protection Technologies
Electronic protection innovations have come to be significantly advanced, supplying ingenious remedies to attend to the ever-growing challenges faced by people and companies alike. From biometric authentication to the assimilation of artificial intelligence and maker learning, these patterns hold the promise of enhancing protection steps in extraordinary methods.Rise of Biometric Authentication
With the boosting requirement for protected and practical verification approaches, the increase of biometric authentication has revolutionized the way people gain access to and protect their delicate information. Biometric verification uses special biological qualities such as fingerprints, face features, iris patterns, voice recognition, and also behavioral traits for identification verification. This innovation offers a more reliable and protected approach compared to typical passwords or PINs, as biometric information is extremely tough to replicate or swipe.Among the crucial advantages of biometric authentication is its ease. Users no more require to keep in mind intricate passwords or fret regarding losing accessibility due to neglected credentials. By merely utilizing a component of their body for verification, individuals can swiftly and safely gain access to their tools, accounts, or physical spaces.
Additionally, biometric verification boosts safety by supplying a more robust defense against unauthorized accessibility. With biometric pens being unique per individual, the danger of identification theft or unapproved access is significantly lowered. This enhanced level of safety and security is especially important in industries such as finance, health care, and federal government where safeguarding delicate info is paramount.
Integration of AI and Maker Knowing
The evolution of electronic protection innovations, exemplified by the increase of biometric verification, has actually led the way for innovations in the assimilation of AI and Artificial intelligence for improved identification and security devices. By leveraging AI formulas and Artificial intelligence models, digital protection systems can currently analyze huge amounts of information to spot patterns, anomalies, and prospective dangers in real-time. These innovations can adjust to advancing safety and security risks and offer proactive reactions to reduce dangers effectively.One substantial application of AI and Machine Learning in electronic safety remains in predictive analytics, where historic data is utilized to forecast prospective security violations or cyber-attacks. This aggressive method permits protection systems to expect and prevent risks before they take place, improving total security actions. Furthermore, AI-powered monitoring systems can smartly keep track of and evaluate video clip feeds to identify suspicious activities or people, improving action times and reducing duds.
IoT and Smart Safety And Security Tools
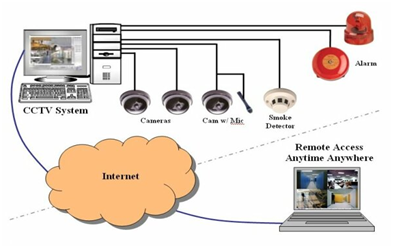
Developments in digital protection technologies have brought about the introduction of IoT and Smart Security Instruments, reinventing the means safety and security systems run. The Web of Things (IoT) has made it possible for protection tools to be adjoined and remotely available, using improved monitoring and control abilities. Smart Safety Gadgets, such as smart cams, door locks, and movement sensing units, are geared up with functionalities like real-time signals, two-way interaction, and assimilation with various other wise home systems.One of the substantial benefits of IoT and Smart Safety Instruments is the ability to provide individuals with smooth accessibility to their safety and security systems through smartphones or various other internet-connected devices. This benefit permits remote surveillance, arming, and disarming of protection systems from anywhere, giving property owners with satisfaction and flexibility. These devices typically include innovative attributes like face recognition, geofencing, and task pattern acknowledgment to improve overall safety levels.
As IoT continues to advance, the integration of artificial intelligence and artificial intelligence algorithms into Smart Security Instruments is anticipated to more enhance detection precision and modification options, making electronic protection systems much more efficient and reliable.
Cloud-Based Safety Solutions
Arising as a critical facet of modern digital safety and security framework, Cloud-Based Safety Solutions offer unmatched flexibility and scalability in guarding electronic possessions. Cloud-based safety solutions enable remote tracking, real-time informs, and streamlined monitoring of protection systems from any type of place with an internet connection.Furthermore, cloud-based protection solutions provide automatic software program updates and maintenance, making sure that safety and security systems check my site are constantly current with the most current defenses versus emerging dangers. In general, get redirected here cloud-based safety and security remedies stand for an economical and effective means for companies to boost their safety pose and shield their electronic assets.
Emphasis on Cybersecurity Procedures
With the increasing refinement of cyber hazards, organizations are placing a paramount focus on strengthening their cybersecurity actions. BQT Sideload locks. As modern technology breakthroughs, so do the approaches utilized by cybercriminals to breach systems and swipe sensitive info. This has prompted organizations to spend greatly in cybersecurity measures to safeguard their information, networks, and systems from malicious attacks
One of the vital patterns in cybersecurity is the adoption of advanced security procedures to safeguard data both at rest and in transit. Security aids to ensure that even if data is obstructed, it remains unreadable and safe. Additionally, the application of multi-factor verification has ended up being significantly common to add an added layer of protection and validate the identifications of users accessing sensitive information.

Verdict
Report this wiki page